OpenVPN integrates well with Active Directory and Active Directory Certificate Services, providing a low-cost, dual factor VPN solution for Windows clients. Dual factor OpenVPN with Active Directory and Certificate Services
This HOWTO uses CentOS 5.3, the latest “stable” OpenVPN package 2.0.9, and assumes you already have AD and Certificate Services running. This VPN configuration is a bridge, meaning users have full TCP/IP access to the internal network once connected.
We will cover configuration in four main parts:
Part 1 - Base OS install
Part 2 - AD Integration
Part 3 - OpenVPN installation
Part 4 - Client Setup
Sample configurations will be included as a fifth part.
1 Base OS Setup
The goal is to make this appliance light. But for ease sake, not every package has been removed. This is a tight box, but not ultra-light. This box has no GUI, it is command line only. Knowledge of vi is recommended.
If you really need step-by-step screen shots, I may add later.
1.1 Base Configuration:
This machine needs two NICs. The drives are mirrored.
1.2 Networking
Two NICs are configured for different networks…disable ipv6 because it is not needed. The default gateway should be your EXTERNAL nic’s gateway. DNS should be your INTERNAL DNS address.
1.3 Disk format
Disk does not need to be more than about 5GB. Split off /var so that logs to not clobber the VPN. Not seen here is the /boot partiion which is about 100MB.
1.4 Packages
This build is based on CentOS 5.3, which is Redhat Enterprise 5.3 upstream.
The packages installed initially include
Applications > Editors (vi enhanced)
Servers > Windows File Server
Base > Admin Tools (not needed)
> Base (took out wireless tools, ypbind, Bluetooth, infrared references)
> System Tools (take out Bluetooth, vnc references)
CentOS Extras > Yum Utilities
Additional packages will be needed for OpenVPN, but will be added later: bridge-utils, samba-common, pam-devel
1.5 After the reboot
After the reboot, setup will run, which appears as a blue-red text box.
Firewall > Disable SELinux and allow port 443 inbound (SSH already allowed). Later, we will make additional firewall changes.
System Services > disable cups, Bluetooth, pcscd, winbind (winbind we’ll start later). Enable ntpd.
Authentication
In the olden days, my (in)experience, authconfig-tui often created a mess, and so I would edit each file needed for the system to use winbind before being joined to the domain. But now, authconfig-tui does a decent job -- though some adjustment will still be needed.
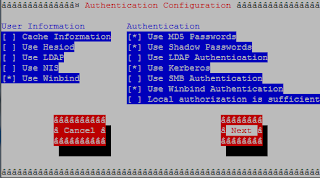
Exhibit 1: authconfig-tui -- windbind should be selected
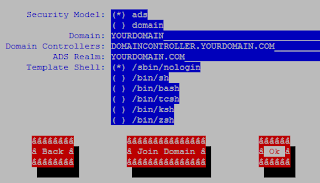
Exhibit 3: winbind will be adjusted later.
Do NOT join to the domain yet. Chances are your clock-skew will not allow it.
Do NOT join to the domain yet. Chances are your clock-skew will not allow it.
When done, close this out. You can get to this page at any time by typing setup.
Install pam-devel + bridge-utils + samba-common (no 's' at the end):
# yum install pam-devel bridge-utils samba-common
Reboot again. You are now done with OS installation. Next, we will join the system to the domain.

No comments:
Post a Comment